Why an investment in people is the best way to protect your organization’s assets
In a highly digital world, cybersecurity threats aren’t new. Despite more and more cybersecurity attacks mentioned daily in the media, companies are still struggling to protect themselves effectively, and their employees are often left in the dark about what they can and should do to help.
Rook Security sees this problem every day with their clients. “While organizations are getting smarter about designing their network and purchasing technology that inhibits a hacker’s ability to take advantage of their systems, they tend not to invest their time into people,” says Tom Gorup, Director of Security Operations at Rook. “However, people are typically where the attacks are sourced from.”

Tom GorupDirector of Security Operations
While there is obviously a concern to protect their employees’ information, employers need to empower their people to know what to do so that they can protect their company’s digital assets — likely, their most important assets. Training your employees will help create that barrier to unwanted entry and is one of the most effective ways to protect your business and its proprietary data.
“People are the first and best line of defense against cyber criminals,” says Gorup. “They’re also often the weakest link.”
How Companies Can Protect Themselves From Cybersecurity Threats
How can companies protect themselves? According to Gorup, it all starts with educating all of their employees — everyone from security, IT, developers, HR, sales, marketing, and all other business units — about at least two things: use of two-factor authentication and creating complicated, secure passwords.
Three well-known cybersecurity attacks are prime examples of where two-factor authentication and secure passwords would have prevented, or at least helped prevent, these attacks from happening:
- Celebrity Hacks: In 2016, many well-known celebrities and public figures — including Drake, Mark Zuckerberg, Kylie Jenner, and more — were hacked after reusing passwords or not having safe, complicated passwords to protect themselves.
- Mat Honan Hack: A senior staff writer for WIRED, Mat’s entire digital presence was destroyed within one hour. His Google account was hacked and deleted, his Twitter account was hacked and “used as a platform to broadcast racist and homophobic messages”, and his AppleID account was compromised, resulting in all of his data on his iPhone, iPad, and MacBook to be erased. This all could have been prevented with the use of two-factor authentication.
- Code Spaces Hack: In the span of only 12 hours, Code Spaces, a code-hosting service, was put out of business due to a cyber attack that resulted in the deletion of the company’s data and backups. Because they didn’t use two-factor authentication, they were forced to close their doors because of the financial burden to repair the situation and lack of credibility moving forward.
“The scary fact is that most people don’t know how to use these or know they exist,” says Gorup. “Password managers and two-factor authentication could save your organization from completely shutting down.”
Password Managers & Password Tips:
“It’s amazing to me how many people use the same passwords everywhere,” says Gorup. “What’s worse is they think their passwords are ‘secure’ when they’re not.”
In fact, 55% of people will reuse their passwords across multiple sites. These passwords need to be reset to strong, complicated passwords for each site.
“Don’t think that just because you changed the I’s in your password to 1’s and the O’s to 0’s that your password is secure,” says Gorup. “Start thinking of passwords as passphrases, increase the length of your password as much as possible, and use a combination of upper- and lowercase letters, numbers, and symbols.”
Creating new, complicated passwords for every new site you use can be cumbersome, and many people worry about how they will remember them. To solve this problem, Gorup encourages people to use password managers, like LastPass, to manage, create, and store their passwords. A well-renowned security expert, Steve Gibson, also gave LastPass his “trust no one” seal of approval.
Two-Factor Authentication:
Gorup also stresses the use of two-factor authentication. “If you are using an app or service that does not offer two-factor authentication or they put arbitrary limitations on your password, complain and complain again,” says Gorup. “Two-factor authentication is critical to protecting your accounts.”
How to Protect Your Email Account, One of Your Most Sensitive Assets
The power of an email account is severely underplayed according to Gorup. “Most people say your cell phone is the worst thing that could get stolen, but I believe it’s actually your email account,” says Gorup.
“Think about everything you access via email: your bank account, social media accounts, Dropbox, Google Drive — the list goes on and on,” says Gorup. “If I can get access to your email account, then I can reset that password for all of those accounts.”
As one of the most important assets you have, your email account needs to be protected. In addition to using two-factor authentication and a strong password, Gorup provides two tips to protect yourself from being compromised:
Don’t participate in polls on Facebook, where hackers can use your information to verify accounts and gain access. “While most polls don’t have malintent, these polls can be used to identify different things about you,” says Gorup. “The name of your first high school, your maiden name, your pet’s name, etc. — typical security questions that are asked when setting up an account — can be used to access your account and exploit you.”
Know how to identify a phishing email. “Attackers will use domain variants similar to well-known domains to send phishing emails,” says Gorup. “The first thing you need to ask yourself is, ‘Are you expecting that email from the organization?’ If not, then you probably shouldn’t be opening it.”
It’s also important to reinspect the domain. For example, someone might use a domain that is similar to GOOGLE.com, but, upon further inspection, the domain is actually GO0GLE.com. Make sure to read the domain carefully.
Finally, before clicking on any links in the email, hover over them and look in the lower right corner of your browser to see the link address. If it looks strange, don’t click on it.
“If it’s a really important matter, the person will call you,” says Gorup. “If the email doesn’t sit right with you, then call them; don’t email them. Attackers will respond back to your email if they can.”
One example Gorup gave was where an attacker had set up an auto-reply to respond to any emails that said, “Is this you? Is this safe?” The auto-responder indicated the email was safe, causing the person on the other end to download a malicious file.
“Always ask who you are you getting your information from and are you expecting it,” says Gorup.
Tips for Employers to Educate Their Employees About Cybersecurity
“It only takes one person to click for your organization to become vulnerable,” says Gorup. “But it’s more important to teach your employees instead of punishing them.”
Gorup shares four tips for employers to help them empower and educate their employees about cybersecurity threats:Don’t embarrass employees when a breach happens.
1. Don’t embarrass employees when a breach happens.
“Don’t put your employees on blast for clicking on an email,” says Gorup. “The last thing you want is for your employees to be afraid to tell you about a potential breach. If you cause embarrassment, people will hide things.”
2. Take a positive approach to user awareness.
“Focus on why security measures will help your employees protect their personal, private information and assets,” says Gorup. “Let them know this is just as much for them as it is your company. If you present it that way, they’ll be much more likely to follow it.”
3. Conduct regular phishing tests.
“After you’ve conducted a user awareness program, validate it,” says Gorup. “Start conducting regular phishing tests to see how your employees handle the emails. Measuring your success and celebrate it within the organization.”
4. Don’t respond with punishment in the event of a breach.
“In most cases, people shouldn’t be fired as a result of a phishing test, or even for a breach,” says Gorup. “We’re not teaching this in high school, middle school, or even college. We aren’t enabling people to know how to handle these situations. Why should they be expected to know it if we’re not teaching it?”
“Cybersecurity education needs to come from all ends. In most cases, it’s a security or IT person leading the charge, but it’s a collective effort to ensure proper security protocols are followed at every level.”
“The bottom line is that we need to make sure people are vigilant when they’re conducting business or personal matters online,” says Gorup. “Effective security is all teams working toward the collective goal to secure the organization.”
Learn More About How to Protect Your Company
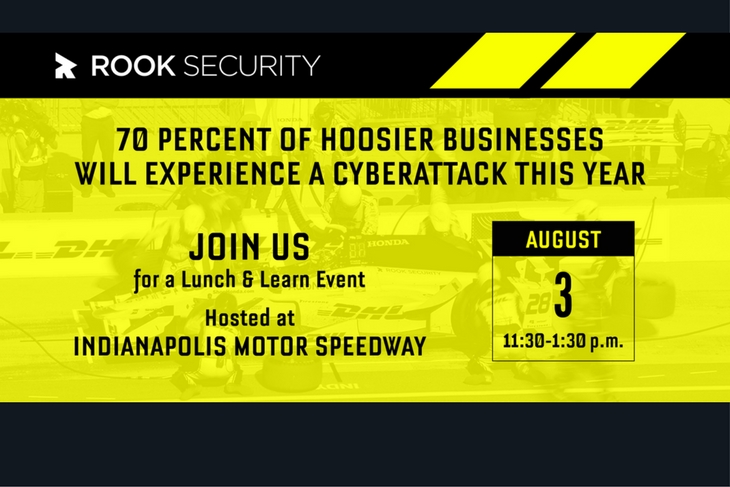
Want to learn more about protecting your business? Join Rook on August 3rd for a Lunch & Learn hosted at the Indianapolis Motor Speedway. Tom Gorup will share actionable steps for combating emerging cyber threats and how to protect your business against even the most sophisticated attacks. Register now.
Can’t join on August 3rd? Sign up for Rook’s Cybersecurity Threat Intel Newsletter to stay up-to-date on the latest cybersecurity news.